Cybercriminals are targeting Linux-based servers running Microsoft’s Azure public cloud environment that are vulnerable to flaws after Microsoft didn’t automatically apply a patch on affected clients in its infrastructure.
Recorded Future reports that the attacks began the night of Sept. 16 after a exploit proof-of-concept was published on GitHub. It was noted that about 10 malicious bot servers have been searching the internet for vulnerable systems. In addition, Cado Security researchers in a blog post also noted a tweet from cybersecurity researcher German Fernandez, who found that the infamous DDoS Mirai botnet – known for taking advantage of insecure Internet of Things (IoT) devices – also is exploiting OMIGOD.
The flaws include CVE-2021-38647, which is a remote code execution bug, and three privileged escalation vulnerabilities: CVE-2021-8648, CVE-2021-38645 and CVE-2021-38649. Ohfeld wrote that the researchers offered a conservative estimate that thousands of Azure customers and millions of endpoints are impacted by the flaws.
“Supply chain cyber attacks have disrupted everyday life and dominated headlines this year,” he wrote. “One of the biggest challenges in preventing them is that our digital supply chain is not transparent. If you don’t know what’s hidden in the services and products you use every day, how can you manage the risk?”
Microsoft was quick to issue fixes to the four vulnerabilities in its September release of security updates, and the vulnerabilities put a spotlight on the risk to supply chains that Microsoft open-source code represents, particularly for organizations using cloud computing services since Microsoft let go its Beta testing teams and community Beta testers that used to volunteer their time.
With OMIGOD, the issue relates to the app called Open Management Infrastructure (OMI), which is embedded in many Azure services and is sponsored by Microsoft open-source OMI project in collaboration with The Open Group.
When users enable any of these popular services, OMI is silently installed on their Virtual Machine by Azure, running at the highest privileges possible. This happens without customers’ explicit consent or knowledge. Users simply click agree to log collection during setup and they have unknowingly opted in to the Microsoft application. Because Azure provides virtually no public documentation about OMI, most customers have never heard of it and are unaware that this attack surface exists in their environment.
The OMI agent operates as root (the highest privileges any users can have) and with it using a Unix socket or through an HTTP API has unlimited control. In Linux, and Unix based environments, the use of Root for any application is discouraged, and this should be the Microsoft default as well, especially when the app is exposed to internet access, but it is not the case as OMI shows. With OMI being so poorly implemented bad actors can easily gain control of the servers.
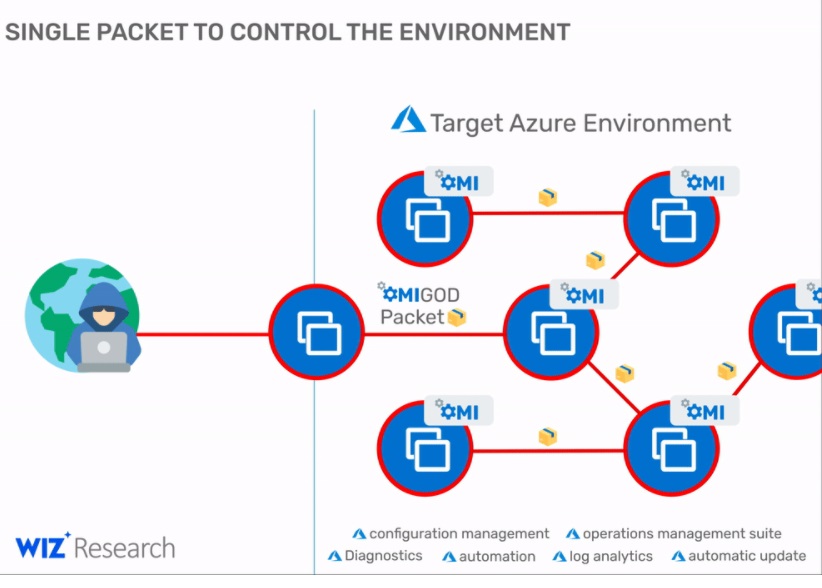
“This vulnerability can be also used by attackers to obtain initial access to a target Azure environment and then move laterally within it,” Ohfeld wrote in a technical blog. Thus, an exposed port with such access privilege's is a holy grail for malicious attackers, and with OMI, one simple exploit provides attackers with access to new targets, execute commands at the highest privileges, and possibly spread exponentially to new target machines.
Recorded Future noted that Microsoft addressed the bug by developing version 1.6.8.1 of the OMI client and releasing it on GitHub, but didn’t automatically install the update on OMI clients in its infrastructure, essentially leaving tens of thousands of servers vulnerable. The company also took three days to replace the OMI client version inside its available Azure Linux VM images.
The cybersecurity firm said a query on the Shodan search engine found more than 15,600 Azure Linux servers connected to the internet, all with possible exposure, and these are just the ones known.
Recommendations
- Immediately implementing the OMI patch.
- Remove it if it is unneeded
- Check and confirm all applications exposed to the internet
- Scan and check all server files, access controls, ports and privilege's as well as check your user accounts and groups.