Bluetooth Classic (BT) protocol is a widely used wireless protocol in laptops, handheld devices, and audio devices. In the past few years, Bluetooth has come under scrutiny due to the discovery of several critical vulnerabilities. In this report, the authors disclose BrakTooth, a family of new security vulnerabilities in commercial BT stacks that range from denial of service (DoS) via firmware crashes and deadlocks in commodity hardware to arbitrary code execution (ACE) in certain IoTs.
As of the report date, 16 different vulnerabilities, which impact billions of devices that rely on Bluetooth Classic (BT) for communication have been uncovered. According to an academic paper from the University of Singapore, the bugs are found in the closed commercial BT stack used by at least 1,400 embedded chip components, that can lead to a host of attack types – mainly denial of service (DoS) via firmware crashes (the term “brak” is actually Norwegian for “crash”). One of the bugs can also lead to arbitrary code execution (ACE).
The team analyzed 13 pieces of BT hardware from 11 vendors; so far, there have been 20 CVEs assigned across them; with four vulnerabilities pending CVE assignments from Intel and Qualcomm. Some of the bugs are patched, others are in the process of being patched; but, researchers said in the paper, “it is highly probable that many other products (beyond the ≈1400 entries observed in Bluetooth listing) are affected by BrakTooth,” including BT system-on-chips (SoCs), BT modules or additional BT end products.
Potentially, billions of devices could be affected worldwide. BrakTooth report by Asset Group
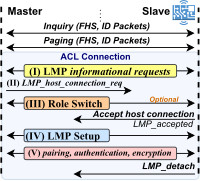
Figure 1: An Illustration of the BT connection procedure. FHS stands for Frequency Hopping Synchronization, ID stands for Identity, LMP stands for Link Manager Protocol and ACL stands for Asynchronous Connection Less.
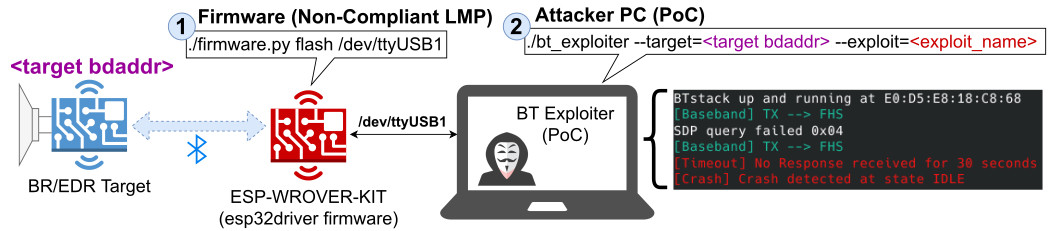
Figure 2: An Illustration of BrakTooth attack scenario
Figure 2 showcases the generic scenario in which BrakTooth attacks are performed. The attacker only requires (1) a cheap ESP32 development kit (ESP-WROVER-KIT [37]) with a custom (non-compliant) LMP firmware and (2) a PC to run the PoC tool. The PoC tool communicates with the ESP32 board via serial port (/dev/ttyUSB1) and launches the attacks according to the specified target BDAddress (
Furthermore, the PoC tool logs over-the-air (OTA) packets and checks the health of the target by getting a paging timeout (no response) or alternatively getting status directly from the target via a serial port, ssh connection, etc.
Researchers successfully forced ESP32 into erasing data housed in devices’ non-volatile random-access memory (NVRAM), which retains data without applied power. They were also able to disable both BT and Wi-Fi on the device; and most concerningly, control the general-purpose input/output (GPIO) of the device if the attacker knows addresses to attached functions-controlling actuators. GPIO is used to communicate the ON/OFF signals received from connected switches, or the digital readings received from connected sensors, to the CPU.
“This has serious implications if such an attack is applied to Bluetooth-enabled smart home products,” the researchers warned.
Second form of atatck - Laptops and devices The second attack scenario can lead to DoS in laptops and smartphones. Researchers were able to achieve this using gear containing Intel AX200 SoCs and Qualcomm WCN3990 SoCs.
One of the DoS bugs (CVE-2021-34147) exists because of a failure in the SoC to free resources upon receiving an invalid LMP_timing_accuracy_response from a connected BT device (i.e., a “slave,” according to the paper:
“The attacker can exhaust the SoC by (a) paging, (b) sending the malformed packet, and (c) disconnecting without sending LMP_detach,” researchers wrote. “These steps are repeated with a different BT address (i.e., BDAddress) until the SoC is exhausted from accepting new connections. On exhaustion, the SoC fails to recover itself and disrupts current active connections, triggering firmware crashes sporadically.”
The researchers were able to forcibly disconnect slave BT devices from Windows and Linux laptops, and cause BT headset disruptions on Pocophone F1 and Oppo Reno 5G smartphones.
A third possible attack - Audio attacks A third attack scenario was discovered while probing various BT speakers (specifically the Mi Portable Bluetooth Speaker – MDZ-36-DB, BT Headphone and BT Audio Modules) and an unbranded BT audio receiver.
They all are variously subject to a series of bugs (CVE-2021-31609 andCVE-2021-31612, failures when sending oversized LMP packets; CVE-2021-31613, truncated packets; CVE-2021-31611, starting procedures out-of-order; and CVE-2021-28135, CVE-2021-28155 and CVE-2021-31717, feature response flooding).
Successful exploits can “freeze” devices, requiring the user to manually turn on unresponsive devices afterwards. For the Xiaomi MDZ-36-DBs and JBL TUNE 500BTs, this can be done while the user is actively playing music, researchers noted.
“Although issues were found in SoCs targeted to audio products, the BT implementation can be reused in a number of SoCs destined to different BT products,” they added.
These are just a few of the possible exploit scenarios.