What is it? Spook.js is a new transient execution side channel attack which targets the Chrome web browser. We show that despite Google's attempts to mitigate Spectre by deploying Strict Site Isolation, information extraction via malicious JavaScript code is still possible in some cases.
In more detail, Spook.js is a fresh side channel attack that works on modern hardware to overcome Google Chrome/Chromium based browsers Site Isolation Protections. The purpose of the aforementioned protections is to prevent each browser tab from being able to see each others memory/storage allocation.
The reason that this is an issue is for example if you are doing something sensitive in one tab, like managing your bank account online, and a separate tab and/or windows you have a different site open that is infected with the spook.js vulnerability. the infected page can potentially read the information from the other tab, such as your banking page.
More specifically, an attacker-controlled webpage can know which other pages from the same websites a user is currently browsing, retrieve sensitive information from these pages, and even recover login credentials (e.g., username and password), especially when they are autofilled. Further the attacker can retrieve data from Chrome extensions (such as credential managers) if a user installs/executes a malicious extension (say when accessing a website with the exploit active).

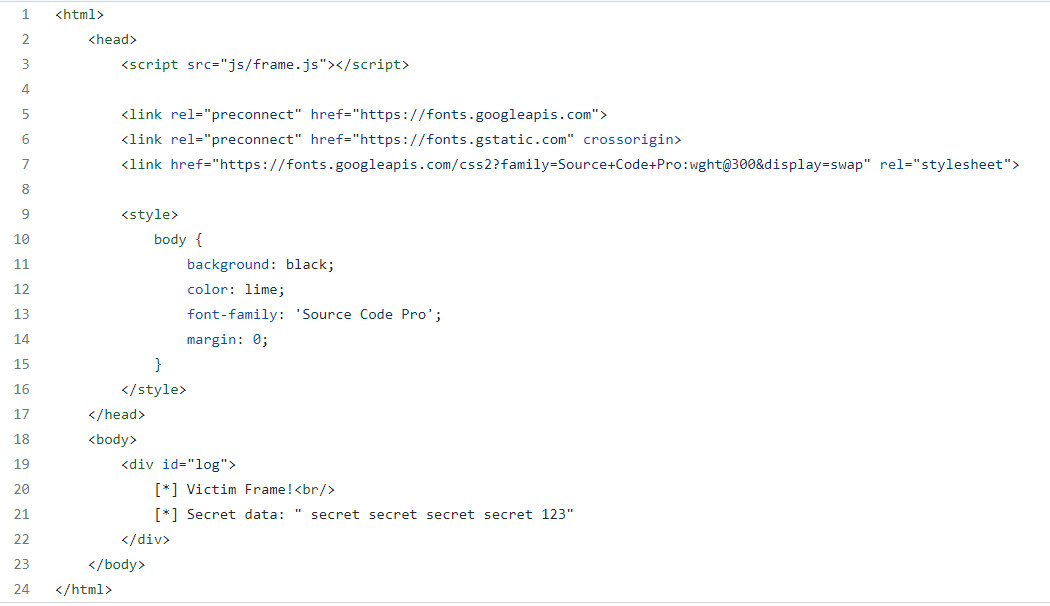 Spook.js Demo 1 - Attacking Credential Managers
Spook.js Demo 1 - Attacking Credential Managers
The underlying vulnerability spook.js exploits though is a previously revealed and currently unresolved hardware issue with all modern CPUs dating back at least 10-15 years ago or so. All CPUs come with a task scheduler that attempts to predict what tasks to run when. if manipulated, said task scheduler can be exploited by using timed attacks on the scheduler to determine what's in memory at the time of the attack.
While this sounds scary, it just means that when browsing sites of a sensitive nature it should be the only tab open on the PC on any chromium browser as long as the sensitive site is open.
This affects all forms of chromium browsers: MS Edge, Opera, Chrome, and others using the chromium code.
Current protection may exist in: Firefox, however, great caution should be used as further testing is on going to confirm, as the advanced settings show mitigation not a fix. So we recommend that the same recommendations below should be used in Firefox also.
Web developers can protect their sites against this exploit, but it is unclear as to when everyone will update the code, and there is no way to confirm if it has been done, so it is best to protect rathe than risk.
The exploit exist on both desktop and mobile devices, so you are not protected just by using your phone.
Recommendations
Be sure your browser is fully patched. Then follow these rules when using any browser.
- Close all browsers to a clean start (as chrome stays active in the background if not fully closed, this is a must) when using anything that requires login information to your sensitive data (office file systems, banking, etc).
- Do not open any other tab or browser while working in the risk sensitive environment
- Close the browser when finished and start a fresh browser for research (being sure to close it if you need to access secure resources).
- Disable autofill, and remove all autofill usernames and passwords.