Owowa is an Microsoft web server (IIS) module currently tuned to intercept outlook web app (OWA) login requests. The exact method of how Owowa makes its way onto servers isn't yet fully known as of publishing of this post, but it is possible that it is deployed as a reconnaissance tool/sniffer during an initial attack on a network. Once it is deployed to a server it is designed to intercept login requests to the target outlook web instance and to funnel the login credentials found to whomever deployed it. This means that if your exchange server is infected, just logging into outlook to check your email can comprise your email account, give the attacker direct control of your email account, and lead to phishing campaigns by pretending to be you. Currently, Owowas targeted have reportedly been governments or government controlled entities in the asia pacific region, but that can change at any time.
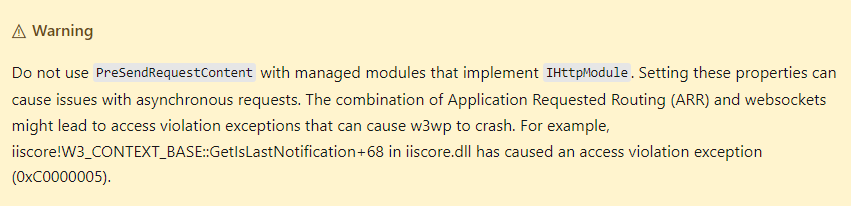
Owowa currently works by monitoring HTTP requests on the infected server and responses for OWA traffic by triggering the “PreSendRequestContent” flag, this flag is suspected to be only triggered when a web application hosted by IIS is about to send content to a client application, such as an outlook client. It also verifies that the login was successful by grabbing data from authentication tokens sent as a access confirmation back to the client which contains the user login credentials, IP address and timestamp. It is suspected that the attacker can enter certain strings into the owa login pages username field on an infected server to retrieve the servers credentials log, delete said log, or use the owa login page password field to remotely execute powershell commands remotely.
The IIS "IHttpModule" is used for packet sniffing. According to Microsoft, using the string with the associated flag triggered within the IHttpModule is not recommended as it can lead to server instability/crashes.
Another part of the danger regarding Owowa is that without having a security regime tuned to looking for the type of traffic that Owowa sends the only real way to determine if Owowa is on your server is a manual investigation of the loaded modules in IIS. We are informed that most/all security platforms are not designed to search for vulnerabilities like Owaowa at the time of this post.
Currently talk about Owowa is just that, talk; even Kaspersky researchers, who first discovered Owowa and made its existence public, have not yet taken any protective action. In addition, there is no current discussion as to what Owaowa can be turned into, since it is a snooping tool for IIS currently tuned to steal exchange credentials, modifications to its programming likely would, and could allow it to grab any sort of data being sent to/from an IIS server. Such a vulnerability could mean that the entire IIS ecosystem is a continuous threat risk.
Part of my concern around Owowa and about how dangerous it can be, is that it has been reported that Owowa has unused empty modules within its code that could be potentially - maybe already have been - could be used to enhance its current capability.
Recommendations
Owowa may not yet be commonplace but the threat is significant enough that immediate action should be taken. Verification of the IIS backend, its configuration, on a regular basis. Checks should be done regularly to look for the module and remove it. It is thought that Owowa is currently a reconnaissance tool for an ongoing attack, post exploit, or information grabber for the dark web that will lead to additional exploits, phishing and scams. So proactive steps need to be implemented to assist in preventing the exploit.