BellaCiao is a the most current advanced trojan host that has come from the group APT35/42 otherwise known as Charming Kitten. This malicious code is made to be highly customizable to pinpoint specific targets, such as specific companies and even subdomains for payload delivery. The actual attack vector is microsoft exchange servers, but without advanced network IDS/IPS systems, BellaCiao could infiltrate your network without detection.
There is no currently known inital infection vector as there is yet to be any publicly stated logging of such. The ininrended target as used by the malwares authors is intended to be infrastructure or other valuble targets with higher than average security.
Upon deployment of the malware on an exchange server, it is currently designed to run the following in powershell.
powershell.exe -exec bypass -c Set-MpPreference -DisableRealtimeMonitoring $true
It then currently starts malicious services in windows to maintain persistence such as:
sc create "Microsoft Exchange Services Health" binpath= "C:ProgramDataMicrosoftDRMSMicrosoft Exchange Services Health.exe" start= auto
sc start "Microsoft Exchange Services Health"
sc create "Exchange Agent Diagnostic Services" binpath= "C:ProgramDataMicrosoftDiagnosticExchange Agent Diagnostic Services.exe" start= auto sc start "Microsoft Exchange Services Health"
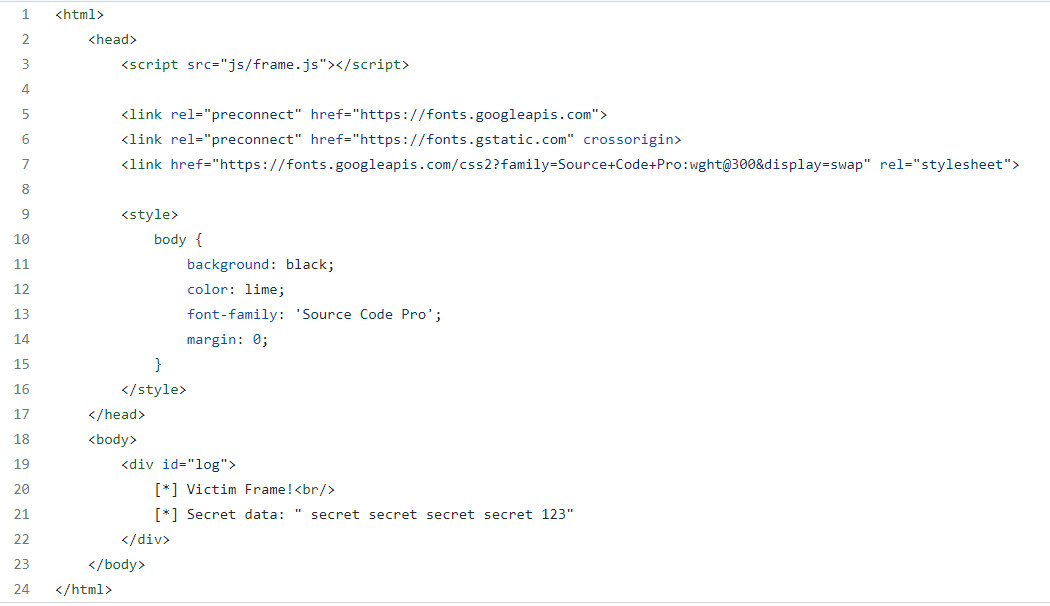
Afterwards its recorded that the culprits then pushed malicious IIS modules to the affected server. one of which was IIS-Raid, an IIS module designed to act as a man in the middle for credential theft, sniffing for passwords in IIS traffic as per a list.
The second module was another custom made module design to exfiltrate the data found by the IIS-Raid module, it also captures and records HTTP requests with keywords “pass”, “pwd”, “password”, or “login” for exfiltration.
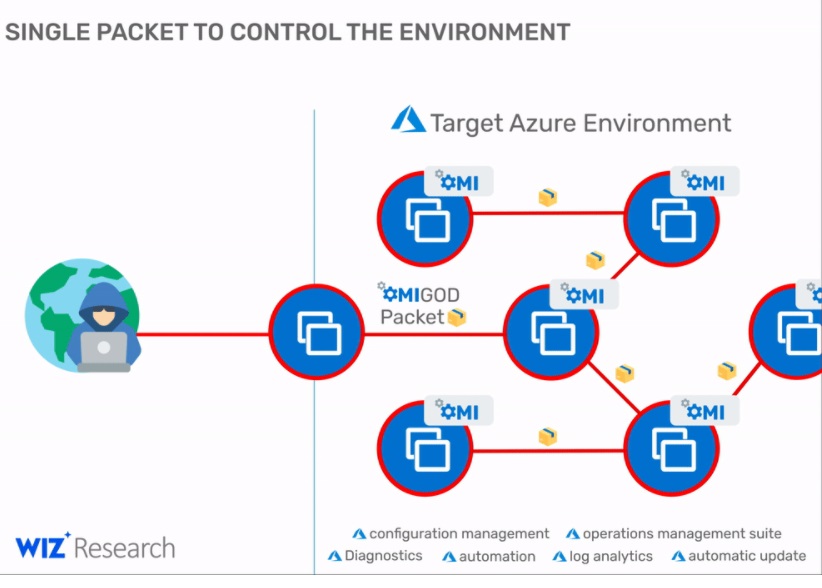
BellaCiao installs itself as a windows service executable to prevent detection by users, and as it is a trojan host and a C2 module, its functions are baked in, and it could also carry a payload within, making it even more unpredictable and dangerous. It sends BNS requests every 24hrs to maintain isn't connection to the internet and the attacker. These DNS requests are sent to a DNS server that the attacker has control of, and the response from the server is how the the commands are sent to act. the last octet in the returned IP determines the actions to take, as per the pre-programmed IPs baked into the code.
Functions possible by this method include:
Command execution
Execute script
Download file
Upload file
Upload web logs
Report web server start time
Report current time
Beep
Stop web server
Assessment:
Our assessment of this type of attack is that more high level and automated tools such as modern IDS/IPS, are needed for an in-depth strategy to monitor network traffic and prevent breaches. This malware platform is attacking exchange servers today, but can likely be rebuilt to attack other types of network resources. Combine that with that it can also infiltrate payloads into a network stealthily means it could possibly wreak more havoc than described in this article today. If you aren't sure if your network security is up to task consult a well known trusted firm to get an assessment of your organization security and have proper polices in place.


 The attacker, however, is using this exploit to retrieve information despite Microsoft considering that this is not how it should be used.
The attacker, however, is using this exploit to retrieve information despite Microsoft considering that this is not how it should be used.